Intel chip flaw: Using digital experience monitoring to assess Meltdown and Spectre patch performance impacts
The Intel chip flaw in AMD, ARM and Intel processors is the latest security concern throwing Silicon Valley into a frenzy. But what is the flaw and what are Meltdown and Spectre, exactly? Here’s the quick and dirty:
The Intel chip flaw consists of a couple of security vulnerabilities giving way to two methods that can expose sensitive information to non-privileged users: Meltdown and Spectre.
Fortunately, Meltdown and Spectre have reportedly not been used in any attacks to date and this may be attributed to the fact that they need specific malware to be effective.
That said, the Intel chip flaw, initially found by Google, exploits speculative execution, a common technique in most Intel processors that predicts likely actions and executes them for a smoother and faster computing experience. Should the prediction be incorrect, the speculative work is thrown out. Both Meltdown and Spectre exploit this feature by bringing user-level visibility into those admin-level actions exposing sensitive information including credentials, cryptographic keys, emails, etc.
Meltdown is an Intel-only vulnerability that exploits Intel’s privilege escalation and speculative execution while Spectre is a vulnerability in Intel, ARM and AMD processors that uses branch prediction as well as speculative execution (Learn more in this Daniel Miessler blog). One of the biggest differences between the two comes from how the issues are patched: Meltdown’s patches are more straightforward, Spectre’s are more complex.
Over the years, we have helped organizations facing numerous vulnerabilities by bringing visibility into the patching process and patch performance impacts through digital experience monitoring. Specifically, our solution, SysTrack, has helped organizations vet and verify Windows updates at times when widespread vulnerabilities have been identified. The result is a smoother patching process while measuring and controlling for poor end-user experience and system performance issues.
Watch this webinar on Digital Experience Monitoring
Although significant vulnerabilities, the Intel chip flaw that has enabled Meltdown and Spectre can be mitigated with proper digital experience monitoring as outlined in the following 3 steps.
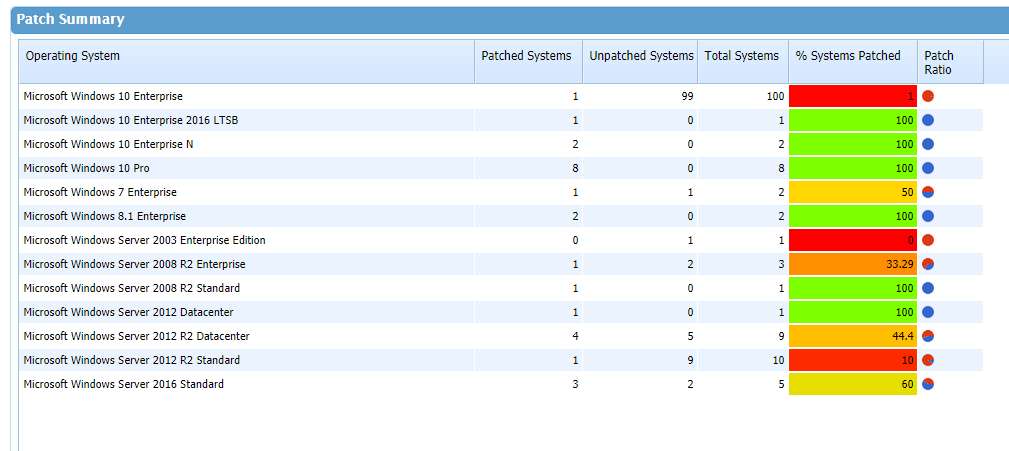
Step 1: Know where you are relative to Meltdown and Spectre
The first step in safeguarding against Meltdown and Spectre is to understand where you stand relative to the flaw. To do that, make sure you have the latest patches once they come out (find Microsoft’s latest fix here).
Fortunately, as of the time of this writing, there are patches for Meltdown and work being done “to harden against future exploitation of Spectre” according to Meltdown Attack.
However, given the nature of this flaw, your risk of exposure will depend on the amount of shared CPUs in your organization and your ability to stay up to date with patching. Given this is a hardware-level vulnerability, only one system needs to be compromised for the attack to be effective in the entire organization.
Step 2: Identify the performance impact
Once the available patches are in place, it’s important to conduct an impact analysis on your environment to identify the impact the patches had on system performance.
As of now, reports on the performance impact of these patches are flying high but the reality is that these impacts cannot be confidently quantified until sufficient data is collected.
However, by properly monitoring system performance directly from your endpoints, you can verify and vet the performance impact any given upgrade has on your end-users and their productivity. From there you can take proactive measures to reduce poor end-user experience.
Step 3: Continue to monitor your environment
As is true with most vulnerabilities, both Meltdown and Spectre require specific malware to be effective. Continue to monitor your environment for abnormal behavior in usage and performance such as: CPU, end-user experience, hard drive space, network activity and more.
Using SysTrack to take your three steps
Though not exhaustive, these three steps can set the foundation for a strong methodology against the Intel chip flaw. If you use a solution like SysTrack for digital experience monitoring, make use of endpoint visibility into your environment to minimize any impacts Meltdown, Spectre and their patches can have on your environment and end users.
Subscribe to the Lakeside Newsletter
Receive platform tips, release updates, news and more